In the world of security, many things have changed since the last release of ACF2 and Top Secret. Credential-based attacks are up - compromised credential-based attacks cost organizations $4.67m annually, while being the initial attack vector 10% of the time[1]. Phishing based attacks cost organizations $4.8m annually, while being the initial attack vector 16% of the time[2].
Additionally, as part of zero trust practices, many companies implement a “never trust, always verify” and “always assume breach” philosophy. Even though many organizations work with this philosophy, the average time to contain a breach is 276 days[3].
Broadcom ACF2 and Top Secret Version 17.0 provide the necessary controls for mainframe identity and access management, enabling organizations to protect against today’s security threats. The security of yesterday is not the security of today or tomorrow.
ACF2 and Top Secret Version 17.0 Pillars
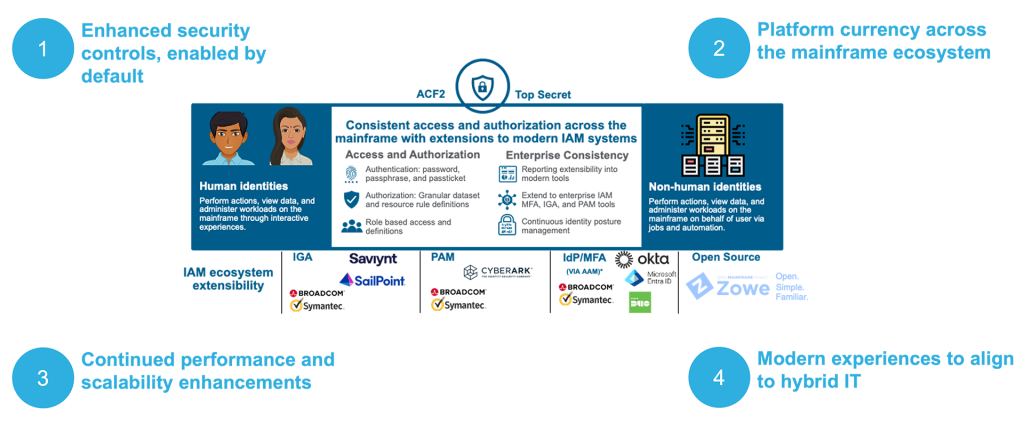
ACF2 and Top Secret Version 17.0 are predicated on four key pillars that enable secure access and authorization for both human and non-human identities:
- Enhanced security controls, enabled by default.
- Platform currency across the mainframe ecosystem.
- Continued performance and scalability enhancements.
- Modern, secure experiences to align to hybrid IT (bridging mainframe and distributed IAM).
Although individual results may vary, as a datapoint realized through the pre-GA process for ACF2 and Top Secret, the migration process from Version 16.0 to Version 17.0 typically took less than an hour, on an LPAR, for a number of participants in the pre-GA program.
Enhanced security controls, enabled by default
To enable mainframe security to meet the security posture of today and to be prepared for tomorrow, key changes have been made to ACF2 and Top Secret in Version 17.0.
Top Secret
With Top Secret Version 17.0, ACIDs must be set with a passphrase/password or be set to PROTECTED. For more information on best practices to mitigate and address NOPW use, please see the published Broadcom STIG article.
In Top Secret Version 17.0, the control option for NOPW has been removed. NOPW allowed ACIDs to log into mainframe resources without a password. Initially, NOPW was intended for started (STC) tasks; however, as enterprise security evolved over time, the NOPW option was exploited for user ACIDs, creating additional security exposure since these ACIDs could perform interactive logins.
It is critical that NOPW be addressed prior to migrating to Top Secret Version 17.0. If ACIDs are still set with NOPW, login will be denied, potentially breaking business processes that are dependent on those specific ACIDs.
ACF2
In ACF2 Version 17.0, it is recommended to address JOBFROM privileged Loginid to ensure proper surrogate checking is enabled and set.
Addressing this in the process of migrating to ACF2 Version 17.0 allows the JOB being submitted by the JOBFROM privileged Loginid to be scoped and accounted for so proper enforcement and auditing is possible. For more information on best practices to address JOBFROM, please see the published Broadcom TechDoc. Without addressing this, a job that is run under a Loginid different from that of the submitter can submit a job, without the submitter providing a password.
Additionally, to align with both distributed and mainframe password policy enforcement, ACF2 Version 17.0 supports additional characters for passphrases. Enterprises can now align the configurability of Active Directory password policy to be consistent with ACF2 password policy enforcement.
In the process of migrating to ACF2 and Top Secret Version 17.0, it is recommended to adopt quantum resistant encryption with AES256 for passwords and passphrases. Both ACF2 and Top Secret support AES256 and it is a critical factor in enabling quantum readiness and positioning for the security of tomorrow.
Platform currency across the mainframe ecosystem
With the release of ACF2 and Top Secret Version 17.0, day 1 toleration and support are critical given the foundational security controls ACF2 and Top Secret provide. IBM z/OS 3.2 is fully supported with ACF2 and Top Secret Version 17.0 along with the latest versions of IBM CICS and IBM Db2.
The compatibility matrix provides the most up to date product compatibility information for both ACF2 and Top Secret:
As new releases of subsystems relevant to the mainframe ecosystem software are delivered, ACF2 and Top Secret will continue to align in providing day 1 toleration and support.
Continued performance and scalability enhancements
As business processing gets more granular and the scale of calls that depend on ACF2 and Top Secret increase and get referenced from distributed systems, the need to meet that scale required changes in control block properties. Workload profiles continue to change as enterprises evolve their use of mainframe systems.
Top Secret
Within Top Secret a few changes have been made to help align to the performance and scale needs of today’s workloads.
The first is re-organization of the RCVT and SKPL control block. If these control blocks are being leveraged, exits referencing these will need to be updated.
Second, by default, the max ACID size is set to 2048. This means all ACID sizes will default to 2048, new and existing. AESCACHE control option is on by default, helping customers using AES256 to maintain performance thresholds.
Lastly, a set of control options have been removed due to the nature of their use and no longer being relevant in today’s security requirements.
More details can be found in the Top Secret R17 tech docs.
ACF2
Within ACF2, the ACFASVT control block size has been increased to 31-bit storage. In cases where there are compatibility issues with applications reliant on 24-bit storage, there is an option to revert to 24-bit storage.
More details can be found in the ACF2 R17 tech docs.
Modern, secure experiences to align to hybrid IT (bridging mainframe and distributed IAM)
As ACF2 and Top Secret Version 17.0 are released, the foundation is set for the next set of modernization activities including delivering true RESTFul APIs to bridge mainframe and distributed IAM experiences. As an introduction to API support, post ACF2 and Top Secret Version 17.0 release, both ACF2 and Top Secret will enable RESTFul APIs to allow for self-service password reset automation – more details to come in a future blog. Additional use cases will expand based on customer feedback and needs.
An additional aspect to bridging mainframe and distributed IAM is ensuring ACF2 and Top Secret work with the broader enterprise security toolset, streamlining integrations to perform lifecycle management and provide added security controls. As an example, Sailpoint with ACF2 and Sailpoint with Top Secret (an Identity Governance and Administration tool) could be used to provision/de-provision identities and entitlements into the mainframe. Another example is increasing security with multi factor authentication (MFA) via Advanced Authentication Mainframe (Broadcom AAM) to connect into MFA providers such as Okta or Microsoft Entra ID.
Additional enhancements in ACF2 to simplify administration include:
- The ability to support &LID in resource rules, reducing the number of resource rules that need to be authored. An example application of this is streamlining Broadcom Trusted Access Manager for Z resource rules line authoring, allowing for self-elevation privileged access management.
- The ability to list LID roles in a single command, instead of having to issue two separate commands to see what roles a LID belongs to.
Enhance enterprise security with the Broadcom Mainframe Security Suite
ACF2 and Top Secret now come with entitlements that help enterprises secure mainframes more efficiently, enforce Zero Trust, and modernize operations. ACF2 and Top Secret set the security foundation that allow enterprises to build a more robust security posture with:
- Cleanup aims to allow enterprises, with confidence, to reduce the security risk posture by removing excess, orphaned identities and permissions that are no longer required for business processes.
- Advanced Authentication Mainframe (AAM) enhances security and aims to help enterprises meet compliance through the ability to add multi factor authentication (MFA). AAM can help thwart attack vectors using compromised credentials as well as phishing-based attacks.
- Trusted Access Manager for Z (TAMz) provides privileged access management enforcement and auditing to enable time-bound, granular, and least privileged access controls. TAMz can help mitigate insider threat attack vectors.
- Compliance Event Manager (CEM) provides real-time alerting, security and system file integrity monitoring, and integration with a SIEM (like Splunk software) to capture and alert on anomalous activities and auditing proof. CEM allows for continuous monitoring to help capture all relevant events – assume breach and collect to remediate breaches.
- Mainframe Security Insights Platform (SI) automates data collection and provides automated reporting capabilities to use for audit activities and ad-hoc business intelligence needs.
As we deliver modern security with ACF2 and Top Secret Version 17.0, we are excited to partner with our customers and ecosystem vendors to enable security for the most critical enterprise assets.
Broadcom also offers Expert Change Planning (ECP) services, allowing customers needing help to work with Broadcom Support and SMEs to enable a smooth migration, if needed. To start the ECP process, please reach out to your sales representative or register for ECP services.
Learn more about Version 17.0 and the related mainframe security offerings by visiting the techdocs and education resources, which includes best practices in migrating from Version 16.0 to Version 17.0.
The product announcement provides additional details, including the lifecycle for ACF2 and Top Secret Version 16.0.
- ACF2: https://support.broadcom.com/web/ecx/support-content-notification/-/external/content/ReleaseAnnouncements/0/36887
- Top Secret: https://support.broadcom.com/web/ecx/support-content-notification/-/external/content/ReleaseAnnouncements/0/36888
[1] https://ibm.com/reports/data-breach

